Introduction to carding bussiness in 2024 ⚠️ Carding in 2024 is not simple; you must invest a lot of time if you want to succeed and make money. If you read our most recent carding tutorials and articles, I can promise you after a week of diligent practice, you will be an expert carder.
STEP 0: CLICK HERE HOW TO CHOOSE NON VBV CC

introduction to carding

Read our updated 2023 comprehensive carding guide for beginners to see how carding has become more sophisticated than ever before and what you can do about it. You will be able to understand how the carding ecosystem functions and how lucrative the carding sector is after reading through this entire tutorial on carding.
ACCESS LEGIT VENDOR STORE!
This ad is last verified on TODAY
✅Begin Your Carding Adventure — — — CLICK HERE
🌐Secure Shopping — — — CLICK HERE
💸Follow the Path to Success — — — — — CLICK HERE
💡 Learn carding online CLICK HERE
☎️24/7 Support — — — — — — — — CLICK HERE
One of the most popular and practical cash alternatives, the use of credit cards as a form of payment has been rising quickly. The general populace of nearly all the major geographic regions on our planet can currently use this method of payment. Its portability and ease of usage make it a favoured method of financial transaction. Without a huge networked ecosystem made up of nodes of various online systems, such efficiency cannot be attained. However, there are hackers and carders everywhere there are computers and networks.
carding Payment card frauds involving credit and debit cards have caused users to seriously worry about their privacy and legitimacy. Recently, several large retail chains, e-commerce websites, and brands have been victimized by these frauds, making the situation worse. The significant financial gain associated with this theft has drawn the largest internet crooks and hackers to create their own empire with a well connected gang of people and organizations. The majority of significant payment card frauds are financially motivated and take several months to complete, starting with the theft of user information and ending with actual fraud. This carding course goes into the specifics of how the entire carding ecosystem works and how it is substantially upending the existing electronic payment sector.
Don’t miss this trending method instant cashout: bitcoin carding method 202444
key terms used in introduction to carding
Let’s begin by reading through a few of the major terms that will be used throughout this carding tutorial and that will be important in further elaborating on the major discussion points.
Describe carding.
Carding is the act of illegally accessing a card’s data and exploiting it to commit fraud for one’s own benefit. I will admit that carding is not simple, and success depends on having the appropriate cc and bin information. However, as everything is offered here, you don’t need to worry.
Who are Carders?
A carder is someone who purchases credit cards from credit card merchants, purchases credit cards from credit card shops, or even purchases credit cards from credit card dumps via the dark web in order to card online retailers.
How do credit/debit cards (ccs) work?
What are CC/Debit Cards, Bins, and Types of Cards? is our first topic. types of credit and debit cards, or the first digit of each;
Every credit card issuer begins their credit card number with a special number to identify them specifically, as is demonstrated below.
What is a PIN (Personal Identification Number)?
a unique numerical identifier used to verify the cardholder.
What are CVV and CVV2?
Number printed on the card, either 3 or 4. As a supplementary means of confirming the cardholder, this number is used.
What is a BIN (Bank Identification Number)?
The card’s first six digits are used to identify the issuing bank and, in some circumstances, the kind of card.
DONT FORGET TO READ ABOUT COMPLETE LIST OF CARDABLE WEBSITE 2024
What is the meaning of BIN (Bank Identification Number)?
refers to the approved businesses whose network is used to enable communication between the acquirer and the issuer. Visa, Mastercard, and American Express are popular brands (Amex). A Visa card begins with a 4, a Mastercard card with a 5, and an Amex card with a 3 (15 numbers long). Later in the publication, a detailed list is presented.
What is a consumer or buyer?
the cardholder who makes the purchase and pays with the card.
What does a “merchant” do?
a seller of goods or a provider of services who accepts cards as payment.
What is an Acquirer Bank?
the bank in charge of handling credit card transactions between the merchant and the customer.
What exactly is an acquirer bank?
the financial institution that issues consumer credit cards.
An Issuer Bank is what?
The bank that issues the consumer’s credit card
What does “Point of Sale” (POS) mean?
The payment transaction between the customer and the merchant is completed by POS machines, which read credit and debit cards.
Point of sale (POS):
The payment transaction between the customer and the merchant is completed by POS machines, which read credit and debit cards.
What is a Magnetic Strip?
the credit/debit card’s black backside strip where various information needed for transactions is stored.
What does a Track mean?
Tracks 1, 2, and 3 store data on the magnetic strip. In most cases, the first two tracks are utilized to hold information like the account number, owner name, etc. It is optional to use the third track, which is used to store extra data.
What is a “Card dump”?
the unencrypted raw data that was taken out of POS machines’ RAM, or temporary storage. These dumps contain data that is written on tracks 1 and 2 and read by the POS device during transaction processing.
What does a runner do:
the person or organization that withdraws money from ATMs using fake identification.
How do I use a card reader/writer?
is a combination of hardware and software used to write data to the plastic card’s magnetic strip. The most often used encoder for writing data across cards is MSR-206.
How does Card Dropper work?
the location where internet purchases are delivered. Typically, the Dropper is a person whose primary responsibility it is to pick up the ordered item and deliver it to the carder in exchange for money or other items.
What exactly is a shopper?
is the person or group that uses fake cards to make in-store purchases. To make the fraud appear more real, some shoppers also have false IDs. Typically, the carder is also a runner or shopper.
EMV: What is it?
Alternatives to swipe cards include EMV or Chip-and-Pin cards, which store data on a chip in an encrypted form. The data can still be stolen by POS-based malware once it has been decoded in memory even though the storage method is encrypted.
Contactless RFID cards are what:?
Adding another improvement to conventional cards with magnetic stripes. With RFID-enabled cards, the customer can make a purchase by wavering the card in front of the POS machine.
HOW CREDIT CARDS PAYMENTS PROCESSED
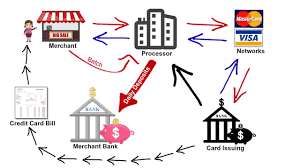
Before the payment is completed, there are multiple processes in a credit card transaction. The primary actions taken during a credit card transaction are listed below:
BELOW ARE TWO CREDIT CARD TRANSACTIONS
Card not present transaction
When neither the cardholder nor the credit card are physically present throughout the transaction, it is referred to as a card-not-present (CNP) transaction. Orders placed remotely – by phone, fax, internet, or mail — are the most typical.
Card present transaction
A card present transaction is one in which the customer physically uses their card to engage with the payment device.
HOW ARE TRANSACTIONS authoriSED
Authorization holds are a service provided by credit and debit card issuers whereby the issuer places a hold on the amount authorized by the cardholder, lowering the balance of available funds until the merchant clears the transaction. Authorization holds are also known as card authorization, preauthorization, or preauth (also called settlement)
Authorization: The cardholder requests permission to use his credit card to make a purchase. The merchant contacts acquirers with transaction requests. The transaction requests are subsequently forwarded to issuers by the acquirer via the cardholders’ card brand network. Through the networks of the card brands, the issuer sends acquirers authorisation numbers. After that, acquirers send authorization codes to the merchant. Merchants provide cards with the required goods or services if the transactions are approved.
Batching: Merchants save all of the allowed sales from a given day in one place. At the end of the day, they send the batch to acquirers via payment service providers to get paid.
Clearing: To request payment from issuers, acquirers transfer the batch across the networks of the card brands. The networks of card companies assign each transaction to the appropriate cardholders. Then, through the networks of card brands, issuers transmit the requested amounts to acquirers.
Funding: Through the payment service provider, the acquirer transfers funds to the merchant. After billing the payment, the sum is given to the merchant.
These are merely a summary of the stages involved in processing credit card payments. Although there are other authorization stages required, these four elements are the main cornerstones of the transaction phases.
TOOLS REQUIRED FOR CARDING IN 2024
ADVERTISE 👏👏👏👏👏👏 those intrested to buy my clones
CLONED CARDS RATES
LOW BALANCE
$250 for balance $3k
$350 for balance $4K
$450 for balance $5k
$550 for balance $6k
HIGH BALANCE
$1k for balance $15k
$2k for balance $30k
$3.5k for balance $50k
$5k for balance $ 70k
You don’t need no Pc or any hacking knowledge for this❌
All you need is your Phone 📱 to Dm me for your CCC✅✅✅
How to place your order!
– Balance of CCC you need…….?
– What quantity you need…….?
– Receivers nick name ……..?
– Delivery address ……..?
-Contact number……..?
Safe to use anywhere💯
Bulk purchase ✅
World wild delivery 📦
a day delivery 🚚 if you in the States🇺🇸!
2-3days for other countries
Start placing your orders now🦅
@unknownhelper001 on telegram
- Computer/Laptop or your Android
- Socks5 / VPN (Compulsory)
- Mac Address Changer (Not Compulsory)
- CCleaner
- Cc (Credit Card) Where to buy valid cvv Refundable
- M.A.C. Address Changer
- RDP
- CCleaner
- Mobile Phone or P.C.
- DROP
tools decribed as below
Socks or a VPN
Be careful not to mix up socks and VPN. Both are good, however choose SOCKS5 if you can’t afford a high-end VPN. Try to connect your Socks or VPN whenever you are about to start carding. If you don’t reside in the United States, you might not be able to successfully card in addition to disguising your IP address.
Address Changer by M.A.C.
Using the M.A.C. address changer is a necessity for carding. If you want to be a successful carder, you simply cannot do without the M.A.C. address changer. You’ll learn when to use this software when carding as you continue reading.
Media Access Control is what MAC stands for. This is comparable to how each Network Interface Card is different (NIC).
You might quickly alter the MAC address of the NIC with a MAC address changer. The need for safety and anonymity is essential. If you don’t want to be apprehended by the police, don’t forget this.
RDP
The Remote Desktop Protocol is referred to as RDP. This carding instruction will benefit greatly from it. Connecting to the victim’s computer using the CC you are targeting requires it as a necessary condition. Don’t forget to download one; it is just as important as a VPN or SOCKS5.
CCleaner
For clearing cookies and cache from the browser, use CCleaner. You gain an advantage over the carding processes and your browsing history is likewise cleared. Servers can trace your activities thanks to temporary browser files. Although clearing browser cookies may be simple, programs like CCleaner can only get rid of flash cookies that were set without your knowledge.
Mobile device or computer? Disconnect from every Google service if you’re using a mobile device. The smartphone must have a sound processor and at least 2GB of RAM. Before doing anything else, root the phone to improve your security.
Purchase a $30 or less Android phone first if you can’t afford to root your current smartphone. So turn off location access if you’re using a Windows or Mac PC. Disable all location services on your computer if you can.
The shipping address used by the carder when carding is referred to as DROP Drop. You will learn the value of a DROP in this carding tutorial. Allow me to explain;
The order won’t be successfully dispatched if you pay with a US credit card and my shipping location is in Nigeria. However, it is acceptable if you use a US address as your mailing address, such as that of a picker, friend, or relative.
But there are businesses that go by the name “DROP” if you don’t have someone. They can help you ship your items to their location because they are in the US, but you will have to pay extra for that service. The picker will now pick up the carded item and deliver it to your location.
Carding Types
There are three categories/levels of carding, according to professional carders. On the list, they are:
When you don’t have a complete CC, BIN BIN is very helpful. It stands for the first four digits of the credit card number and the bank identification number. Typically, the first six digits are used. For instance, the first four digits of the card number, 6456, which is BIN, are 5466, 6454, and 7456.
You can create a virtual card for carding using the BIN. You would eventually learn how to card at a high level.
CC Specifics
The CC is a crucial component for successful carding. You must spend time learning about CC and its components as a newcomer to carding. Fortunately for you, I will tell you all there is to know about the CC right now.
Credit Card is referred to as CC, but in carding we refer to it as CC details. It’s because you won’t actually get a credit card when you pay for CC. Instead, you’ll get a Virtual Notepad with the credit card information on it.
The three CC types available for purchase are: Full CC, Partial CC, and Conventional CC (CC Fullz)
Processing of CC
Traditional CC
The service CC is the standard, less priced CC that you can typically find online. Due to the lack of details, you can’t utilize it for very many carding procedures. I am limited to working on shoddy websites.
Information in Regular CC
Name:\sState:
Address:\sCity:
post office code
Telephone Invoice Number:
Card Number: Expiration: CVV: Full Full CC
You can use these additional details on credit sites like PayPal.
More CC information is included in the partially full CC, such as:
SSN: Mother’s Maiden: Birthdate Full CC, also known as CC Fullz
Although this CC is relatively pricey, it gives all the information needed to card any platform. You have a good possibility of making more than $50 per week if you can obtain this as a novice and have knowledge of this carding instruction.
Additional information in full CC includes:
Account number, routing number, bank name
Driver’s License Number: Bank Number: Credit Card PIN Statuses of CC
It is a good idea to check the CC balance to avoid wasting any time.
step by step easy carding guide 2024
Make sure you have the following carding tools available before moving on to the next stage.
Credit card, CCleaner software, High-Speed internet, Socks5 (also known as SOCKS5 Proxy), which hides your identity and changes your location to match the address on the credit card, and, last but not least, your VPN (so all your activities gets encrypted and safe).
Make a new email account with the name “CC holder” in it. Make the email address Smithparker78@***.com if Smith Parker is the cardholder. Never use throwaway Emails for carding, please.
If you are not using RDP, perform the following steps to connect to your host:
Using MAC Address Changer, all MAC addresses can be changed.
Using CC Cleaner, delete all of your computer’s history, including the cache and temporary files.
Set up Sock5 in Mozilla Firefox by following the instructions I provided above for setting up Socks in Mozilla.
Restart your browser now, then click this site to see if your IP has changed to match the location of the cardholder.
Open any local online market store, and I’ll advise you to utilize someone from your own nation.
Create a new account with the CC holder’s name and the email address you used for carding.
Never use large orders for your initial transaction; instead, try adding an item to your cart that costs less than $500 USD.
Include the address where you wish to deliver the product in the shipping address field.
Go ahead and select the credit card payment method.
Enter all the credit card information you were given at the time you purchased the card.
Use the address of the credit card holder as the billing address.
Conclusion
In a nutshell, we have observed how the networks for accepting card payments operate. Then we read about the various dangers that these electronic payments face. The behavior of POS malware was then highlighted. The type of information this software steals was then revealed. We’ll now proceed to our actual agenda: How the core of an ever-profitable cybercrime is this stolen information
We appreciate your study of the carding instruction.
ACCESS LEGIT VENDOR STORE!
This ad is last verified on TODAY
✅Begin Your Carding Adventure — — — CLICK HERE
🌐Secure Shopping — — — CLICK HERE
💸Follow the Path to Success — — — — — CLICK HERE
💡 Learn carding online CLICK HERE
☎️24/7 Support — — — — — — — — CLICK HERE